Information Technology
-

 839
839Zara’s Fashion Revolution: How the Brand Transformed the Way We Shop for Clothes
Welcome to the fashion revolution led by none other than Zara! With its rapid rise to success and unique approach to clothing...
-

 1.1K
1.1KUnleashing the Power of Cloud Computing: Storage as a Service
Welcome to the future of computing, where the power of cloud technology knows no bounds! In this digital age, businesses are constantly...
-

 1.1K
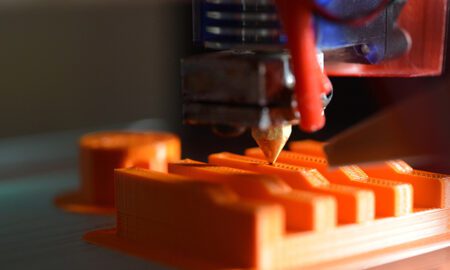
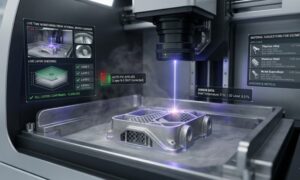
1.1KUnlocking Creativity with 3D Printing Technology: Inspiring Innovations in Art and Design
Step into a world where the boundaries of imagination cease to exist and creativity takes on a whole new dimension. In this...
-

 2.7K
2.7KUnderstanding the Pros and Cons of Different Zoom Accounts
Are you feeling a tad bit overwhelmed with all the Zoom account options available? Well, worry no more! Whether you’re a tech-savvy...
-

 3.2K
3.2KZooming In: Exploring the Various Types of Zoom Accounts and Their Features
Are you ready to take your Zoom experience to the next level? Whether you’re a seasoned pro or new to the world...
-

 1.1K
1.1KThe Power of Zoom: How It’s Transforming Education Worldwide
In a world where distance and geographical barriers were once obstacles to learning, technology has come to the rescue, revolutionizing education on...
-

 2.4K
2.4KHow to Effectively Use Zoom for Remote Meetings, Classes, and Social Gatherings
Welcome to the era of Zoom, where virtual meetings, classes, and social gatherings have become the new norm. Whether you’re a seasoned...
-

 2.3K
2.3KZoom Revolution: How This Platform is Transforming Remote Communication
In an era where remote work and virtual meetings have become the norm, one platform has emerged as a game-changer: Zoom. With...
-

 2.1K
2.1KUnlocking the Power of Zoom: Your Comprehensive Guide to Seamless Communication
Are you fed up with endless commutes to work or school? Longing for a way to connect with colleagues and friends without...
-

 987
987Exploring The Role Of A Podcast Producer In Brand Building And Audience Engagement
Are you ready to tune in and discover the captivating world of podcast production? Get your headphones on and prepare for a...
-

 1.4K
1.4KPodcast Production 101: Must Have Tools And Strategies For Producers
Are you a budding podcast producer ready to take the audio world by storm? Or perhaps an experienced pro looking for some...
-

 965
965The Evolving Role Of A Podcast Producer In The Digital Age
Are you a podcast enthusiast eager to dive into the captivating world of content creation? Or perhaps you’re an aspiring podcast producer...
-

 751
751Mastering the Craft of Captivating Narratives: Wisdom from a Podcast Producer
Are you prepared to unveil the artistry behind crafting narratives that seize the imagination, hold audiences spellbound, and etch an indelible mark?...
-

 791
791How to Become a Successful Podcast Producer: 7 Key Steps
Are you eager to step into the exciting world of podcasting and make your mark as a successful podcast producer? Look no...
-

 10.9K
10.9KCracking The Code Of Exceptional Podcasts: The Expertise Of A Seasoned Producer
Are you fascinated by the world of podcasts and wonder what makes some shows exceptional while others fall flat? Have you ever...
-

 1.2K
1.2KBehind The Scene With A Podcast Producer: What They Do And Why It Matters
Lights, camera, action! Have you ever wondered what goes on behind the scenes of your favorite podcasts? The magic that brings those...
-

 881
881The Power Of Podcast Producers: Elevating Your Show From Good To Great
Are you ready to take your podcast from good to great? Well, you’re in luck because today we are diving into the...
-

 919
919Unlocking The Secret Of Podcast Production: A Deep Dive Into The Mind Of A Producer
Have you ever wondered what goes on behind the scenes of your favorite podcasts? How do they come up with captivating content,...
-

 1.4K
1.4KFrom Concept to Soundwaves: How a Podcast Producer Breathes Life into Audio Content
Are you ready to dive into the fascinating world of podcasts, where stories come alive and voices transport us to different realms?...