Today’s software release cycles happen more frequently than ever before. Many DevOps teams now deploy multiple times per day, pushing out updates, fixes, and features over and over again.
But speed alone doesn’t necessarily equal progress. With greater release velocity, risk also increases, especially without adequate release management controls. More frequent changes mean more opportunities for misconfigurations, regressions, and security gaps to reach production.
This is one of the reasons we continue to see a steady stream of software vulnerabilities, even from mature engineering teams.
The goal for release management in 2026 is no longer just speed. It’s predictable, low-risk delivery at scale. There’s an important distinction here. Speed is about how fast you can push changes. Scale is about how consistently and safely you can deliver changes across environments, users, and systems without introducing instability.
That is the main differentiator today between teams that just ship fast and those that deliver reliably at scale. Here are four strategies teams can use to make that shift.
Progressive Delivery Over Big Bang Releases
“Big Bang” releases have long been the norm in software deployments, where all users receive major updates all at once. But this approach comes with a significant downside: a large blast radius. If something breaks, it breaks everywhere. It made sense when release cycles were slower and teams had time to validate changes thoroughly before deployment, but it doesn’t fit the reality of modern, high-frequency release environments.
Progressive delivery offers a much safer alternative. Instead of releasing changes all at once, teams roll them out incrementally to smaller subsets of users or systems. This can start with internal users, then a small percentage of customers, and gradually expand as confidence increases.
The main advantage is real-world validation. Many issues arise post-production, simply because staging environments can’t fully replicate real traffic. By safely discovering, validating and remediating issues under real conditions, the cost of failure also decreases, as problems are contained to a small subset of users rather than impacting the entire system.
Techniques like canary deployments and feature flags are worth considering here. Canary releases allow teams to expose new versions to a small percentage of users first (for example, 5%), while feature flags provide control over what features are available to specific users, groups, or environments without requiring a new deployment.
Build Reliable Rollback and Recovery Mechanisms
No matter how mature your release process is, failures are inevitable. What separates high-performing teams from the rest is not whether incidents happen, but how quickly and
effectively they recover. This is why modern release management places a strong emphasis on MTTR (Mean Time to Recovery).
Fast recovery starts with treating rollback as a core part of the release strategy. Too often, teams focus on shipping changes into production as quickly as possible, without ensuring there is a clear path to revert them when something goes wrong.
“Blue-green deployment” is a strong rollback strategy. This is where teams maintain two identical environments and switch traffic between them, allowing for near-instant rollback by redirecting users back to the stable version if issues arise. However, this strategy is not ideal in environments with active transactions or complex database dependencies.
The best approach takes us back to designing releases as smaller, incremental, and reversible changes, also known as a zero-downtime release strategy. Updates are split across multiple stages, such as adding new fields, supporting both old and new logic in parallel, and only removing legacy components once the new version is validated.
The system remains operational throughout the process, and each step can be safely rolled back without data loss or inconsistencies.
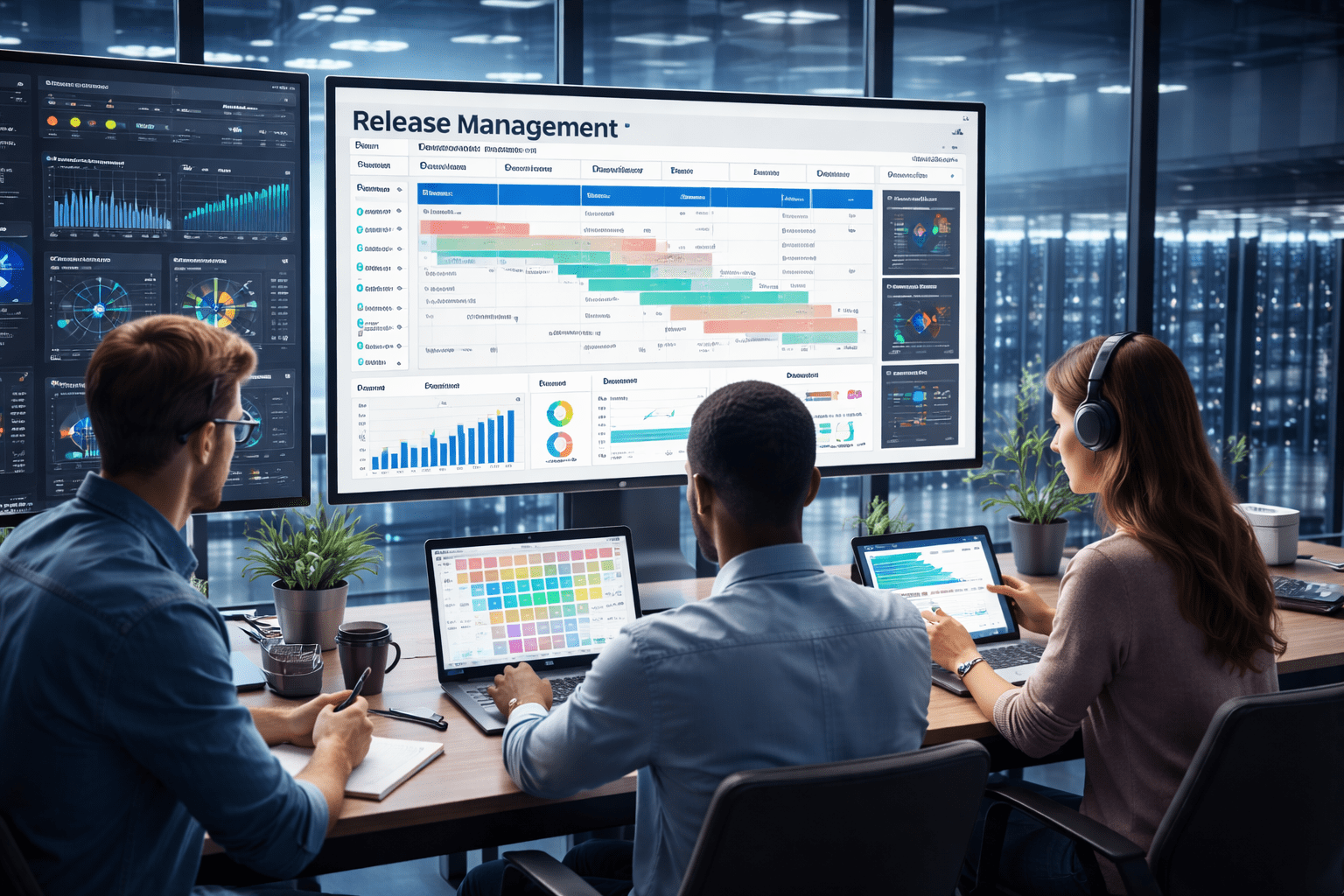
Improve Cross-Team Visibility
Many software failures pop up because of misalignment between security, DevOps, and QA teams. These teams often operate with their own tools and processes, without a shared understanding of release status, risks, and dependencies across the pipeline.
To improve cross-team visibility, those silos must break. Security and DevOps, especially, should not function as separate entities. What they need is clearly defined roles within the same process.
Centralized dashboards are great for providing a real-time view of release status, dependencies, failures, and environment differences across all teams. Dashboards can ingest data from CI/CD pipelines, monitoring tools, and security scanners into a single view, making it easier to spot issues sooner and coordinate faster.
The team should also establish shared ownership of releases. When everyone clearly understands their responsibilities and has visibility into the same information, issues can be identified and resolved much faster.
Shift Validation Earlier in the Pipeline
Catching issues late, during staging or, worse, in production, is a very expensive and disruptive way to manage software quality. By then, changes are harder to isolate, fixes take longer to implement, and user impact is much more likely.
The better approach is to shift validation earlier in the pipeline. Testing and security checks should not be the final gate before release, but a key component throughout the entire software development lifecycle (SDLC).
Automated unit, integration, and regression tests should run continuously with every commit, informing devs of any issues as soon as they appear. Security should follow the same model by embedding security scanning early through static application security testing (SAST), dependency scanning, and secrets detection.
Validation also extends beyond code. Infrastructure configurations, environment setups, and deployment scripts should be tested and verified early, especially in infrastructure-as-code environments.
Conclusion
Speed is not the only benchmark for success in modern release management. There is no point in shipping faster if each release introduces more risk and instability into the system. The most effective teams are the ones that have built processes to manage risk at every stage.
That is not to say that speed doesn’t matter, but it should be the end result of a well-designed and reliable release management process, not the primary goal.