All posts tagged "cybersecurity"
-

 798Artificial intelligence
798Artificial intelligenceMohammad Majharul Islam Jabed Pioneers AI-Driven Cybersecurity with Cross-Industry Expertise
Falls Church, VA – September 17, 2025 – In an era where technological innovation reshapes industries, Mohammad Majharul Islam Jabed stands out...
-

 585Press Release
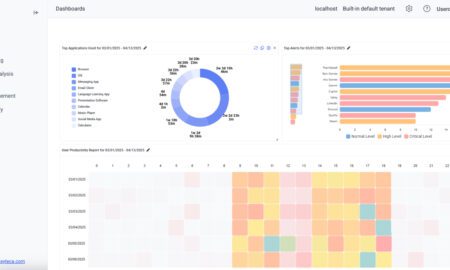
585Press ReleaseNew in Syteca Release 7.21: Agentless Access, Sensitive Data Masking, and Smooth Session Playback
Waltham, United States, 17th September 2025, CyberNewsWire
-

 934Information Technology
934Information TechnologyThe Importance of Reliable Technology Support for Businesses
In today’s fast-paced digital world, every business relies heavily on technology. From managing customer data to securing financial information, smooth operations depend...
-

 576Press Release
576Press ReleaseLink11 Reports 225% more DDoS attacks in H1 2025 with new tactics against infrastructure
Frankfurt am Main, Germany, 9th September 2025, CyberNewsWire
-

 3.1KCybersecurity
3.1KCybersecurityOperating Blind: Kiteworks 2025 Report Reveals How Visibility Gaps Put Enterprises at Risk
Enterprises today face mounting risks as sensitive data moves across clouds, partners, and internal systems. While digital transformation drives speed, it also...
-

 839Cybersecurity
839CybersecurityCybersecurity in Virtual Data Rooms: Lessons from Recent Data Breaches and How to Choose a Secure Provider
Virtual data rooms (VDRs) sit at the centre of highstakes work: M&A due diligence, fundraising, divestments, syndications, capitalmarkets filings, and legal disclosure....
-

 708Technology
708TechnologyWhat Are the Best AI-Powered Cybersecurity Solutions for Large Enterprises?
Adoption of artificial intelligence (AI) is key to boosting corporate cybersecurity. Only some platforms are sophisticated enough to predict vulnerabilities, detect real-time...
-

 1.0KCybersecurity
1.0KCybersecurityCybersecurity Isn’t Optional Anymore: The 2025 Playbook for Mid-Sized Companies to Stay Secure – or Get Burned
Meta Description: A 2025 cyber-security whitepaper for mid-sized businesses. Explore rising threats, regulatory pressures, and how SAV Associates builds resilience with NIST...
-

 637Technology
637TechnologyInterview with David Chen, VP & CTO, DataNumen
This is an interview with David Chen, VP & CTO, DataNumen As the CTO of DataNumen, can you share your background and...
-

 979Cybersecurity
979CybersecurityHow Cybersecurity Startups Can Scale Faster with a Fractional CMO: The 2025 Growth Acceleration Playbook
Cybersecurity startups face unique scaling challenges that go far beyond typical technology growth hurdles, from establishing trust in markets where security failures...
-

 503Business news
503Business newsCybersecurity Services Every Business Should Consider in 2025
In today’s digital-first world, businesses are more connected than ever. While this opens up opportunities for growth, it also increases the risk...
-

 7.1KCybersecurity
7.1KCybersecuritySMBs Face a Dangerous Cybersecurity Conundrum, Study Shows
Smaller businesses know they need to strengthen their cyber defenses. Yet as a new SMB tech report reveals, many lack the resources...
-

 963Technology
963TechnologyNavigating the Web Smarter: How Proxy Services Influence Modern Digital Systems
The internet would appear like an open play area, but underneath the surface lies a compound networking of restrictions, information policies, and...
-

 659Press Release
659Press ReleaseINE Named to Training Industry’s 2025 Top 20 Online Learning Library List
Cary, United States, 11th August 2025, CyberNewsWire
-

 571Business news
571Business newsProtecting Your Business Starts with Your Team – Cybersecurity Tips from James Assali
If you think hackers only go after big companies with millions in the bank, think again. These days, small and mid-sized businesses...
-

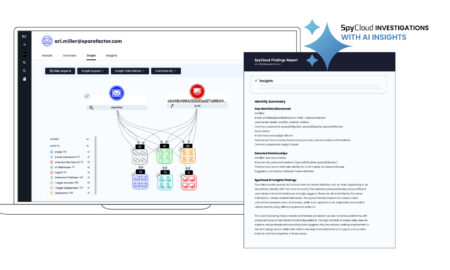
 591Press Release
591Press ReleaseSpyCloud Enhances Investigations Solution with AI-Powered Insights – Revolutionizing Insider Threat and Cybercrime Analysis
Austin, TX, USA, 6th August 2025, CyberNewsWire
-

 379Latest News
379Latest NewsZero Trust or Zero Results? The 80/20 Rule That Defines Cybersecurity Success
In the cybersecurity world, buzzwords come and go. But few have stuck around—and stirred more confusion—than “Zero Trust.” “It’s everywhere,” says Scott...
-

 243Business news
243Business newsHow Cybersecurity Services Protect Against Modern Threats
Let’s be honest—cyber threats are no longer something only large enterprises have to worry about. Today, even small businesses and individuals face...
-

 111Artificial intelligence
111Artificial intelligenceAdvanced AI-Driven Malware Detection and Classification Using Multimodal Security Signals
The increasing volume and complexity of cyberattacks utilizing images, URLs, and QR codes have introduced significant challenges for existing security systems. Traditional...