The Permission You Didn’t Know You Gave
I spent 25 years at IBM building systems that processed millions of transactions per day. Banking systems. Insurance platforms. Logistics networks. In all of those years, one principle never changed: the most dangerous security failure is not a break-in. It is a door left open by the person who owns the building.
That principle applies to cryptocurrency in 2026 more than it ever applied to enterprise IT.
Over the past several months, a growing number of people have walked into OneMiners locations in Prague and New York with the same problem. They connected their wallet to a website. They approved a transaction. They did not understand what they approved. And by the time they realized something was wrong, their assets had moved, not because someone hacked their wallet, but because they had unknowingly given permission for that movement.
This is not a technical failure. It is an information gap. And information gaps are solvable. That is what this guide is for.
How Wallet Approvals Actually Work
Let me explain this the way I would explain a system architecture to a junior engineer — clearly, without shortcuts, and without assuming you already know.
When you use a cryptocurrency wallet, you have a private key. Think of this as the master key to a building. Every door, every room, every safe — one key opens them all. As long as you hold this key and nobody else has a copy, your building is secure.
Now, here is where it gets interesting.
Certain applications — decentralized exchanges, token platforms, DeFi protocols — ask your wallet to “approve” an interaction. On the surface, this looks routine. A small popup appears. You click “Confirm.” It feels like agreeing to terms and conditions.
But what you may actually be doing is handing someone a copy of a specific room key. Not your master key — but a key that says: “You may enter this room and take what you find, at any time, without asking me again.”
The key insight: you are not sending funds. You are granting permission for someone else to move them later. This distinction is critical, because it means the loss does not happen immediately. It happens when the party you approved decides to act.
In enterprise IT, we call this a “standing authorization.” It is the most audited, most restricted permission in any system I ever built. In crypto, anyone can request one with a single popup.
How Deceptive Schemes Use This Mechanism
I am not going to use dramatic language. I am going to describe the mechanics the same way I would describe a system vulnerability in an architecture review — factually and with enough detail for you to recognize it.
The typical pattern:
Step 1: The bait. You discover a new token, a “free airdrop,” or an investment opportunity. It arrives through social media, a messaging app, a forum, or sometimes a token that appears directly in your wallet that you never purchased.
Step 2: The urgency. The message includes a time pressure: “Claim within 24 hours.” “Limited allocation.” “Price increases tomorrow.” In 25 years of enterprise work, I have never seen a legitimate system that required you to make a security decision in under an hour. Legitimate systems wait for you. Illegitimate ones pressure you.
Step 3: The approval. You are directed to a website that looks professional. It asks you to connect your wallet and approve a transaction. The approval request may look standard — similar to what you have seen on legitimate platforms. But buried in the details (which most wallets display in small, technical text) is a permission that grants unlimited access to your tokens.
Step 4: The extraction. Hours, days, or sometimes weeks later, the approved party uses that standing authorization to move your assets. By the time you notice, the transaction is confirmed on the blockchain and irreversible.
Why it works:
This is not about intelligence. I have seen PhDs in computer science make this mistake. The reason it works is that the approval interface in most wallets was not designed for clarity. It was designed for function. The information is technically present, but it is presented in a way that requires expertise to interpret.
That is a design failure, not a user failure.
Warning Signs: The Checklist
In enterprise security, we use checklists. Not because people are careless — because even careful people benefit from a structured review before making a decision. Here is yours:
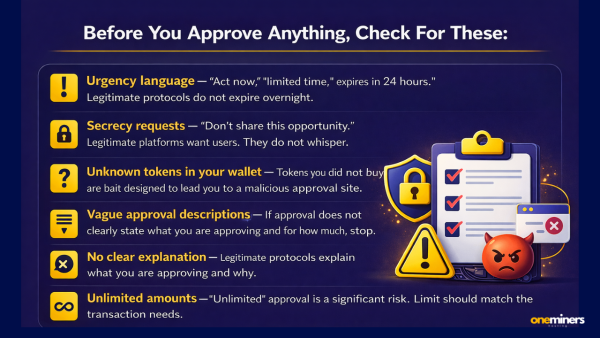
Before you approve anything, check for these:
- Urgency language — “Act now,” “limited time,” “expires in 24 hours.” Legitimate protocols do not expire overnight.
- Secrecy requests — “Don’t share this opportunity.” Legitimate platforms want users. They do not whisper.
- Unknown tokens in your wallet — Tokens you did not buy appearing in your wallet are not gifts. They are often bait designed to lead you to a malicious approval site.
- Vague approval descriptions — If the wallet popup does not clearly state what you are approving and for how much, stop. Read the details. If the details are unclear, do not approve.
- No clear explanation of what the approval does — A legitimate DeFi protocol will explain what you are approving and why. If the explanation is missing or confusing, treat it as a warning.
- Unlimited token approval amounts — If the approval is for an amount far exceeding what the transaction requires (or displays as “unlimited”), this is a significant risk. Limit your approvals to the exact amount needed.
- The website is unfamiliar — Check the URL character by character. Fraudulent sites often differ from legitimate ones by a single letter.
The two-minute rule:
If you cannot explain to someone else — in plain language — what an approval will do and why you are granting it, do not approve it. Close the browser. Walk away. Come back when you can explain it. The blockchain will still be there tomorrow.
What to Do If You Think You Approved Something You Shouldn’t Have
Speed matters here. Not panic — speed.
Immediate steps:
- Do not approve any additional transactions. If a site asks for a second approval to “fix” or “reverse” the first one, that is likely another malicious request.
- Check your active approvals. Tools like revoke.cash or Etherscan’s token approval checker allow you to review and revoke standing permissions. Look for any approvals you do not recognize.
- Revoke suspicious approvals immediately. This costs a small network fee but removes the standing permission. If the malicious party has not yet acted, revoking the approval prevents future extraction.
- Move remaining assets to a new wallet. If you have any doubt about what was approved, the safest action is to transfer your remaining assets to a fresh wallet that has never interacted with the suspicious site.
- Document everything. Take screenshots of the site, the transaction hashes, and the approval details. This information is useful for reporting and for understanding what happened.
Best Practices: Building Long-Term Security Habits
Security is not a one-time action. It is a system. In 25 years at IBM, the organizations that stayed secure were not the ones with the best firewalls — they were the ones with the best habits.
The habits that matter:
Use separate wallets. Keep a “hot” wallet with small amounts for daily transactions and experimentation. Keep your primary holdings in a separate wallet that never connects to unfamiliar websites. Think of it as a current account and a savings account — you would not carry your life savings to the market.
Review permissions regularly. Once a month, check your active approvals on revoke.cash or a similar tool. Revoke anything you no longer need. Standing permissions that are no longer useful are open doors you have forgotten about.
Verify before connecting. Before connecting your wallet to any platform, verify the URL independently. Do not click links from messages or social media — type the address yourself or use a bookmark you created previously.
Use hardware wallets for significant holdings. A hardware wallet requires physical confirmation for every transaction. It adds a step — but that step is the difference between a building with a security guard and a building with an open lobby.
Stay informed. The methods used in these schemes evolve. Following reputable crypto education resources — like btcfq.com, which provides clear, jargon-free guides on cryptocurrency fundamentals — helps you stay ahead of new patterns.
When You Need Someone to Talk To
Here is what I have learned in a decade of working in this space: the most dangerous moment for anyone in crypto is not when they encounter a deceptive scheme. It is the moment after — when they feel confused, unsure what happened, and do not know who to ask.
The internet is full of advice. Some of it is good. Some of it will make the situation worse. And there is something fundamentally different about sitting across from a real person, showing them your screen, and saying: “Can you help me understand what happened here?”
This is one of the things that makes OneMiners genuinely different.
OneMiners operates physical locations where people can walk in, sit down, and have a real conversation about their crypto questions. Not a chatbot. Not a support ticket. A person, in a room, looking at your situation with you.
In Prague: Stop by and speak with the team. Whether you are unsure about a wallet interaction, want someone to review a transaction with you, or simply want to understand how permissions work — having that conversation face-to-face changes everything. They have been handling these questions increasingly in recent months, and the team has direct experience walking people through exactly these situations.
In New York: The same level of in-person support. Bring your questions. Bring your concerns. Bring the laptop if you want someone to look at the screen with you. There is no substitute for having a knowledgeable person in the room.
The staff at OneMiners are not just miners and hardware experts. They understand wallets, transactions, approvals, and the broader security landscape. When five customers came in with the same type of problem within a single month, the team recognized it as a pattern and started proactively educating visitors. That is the kind of response you get from people who actually care about the community they serve.
You can also use asicprofit.com to calculate your mining profitability, and btcfq.com to deepen your understanding of Bitcoin fundamentals — because the better you understand the ecosystem, the harder it is for anyone to mislead you.
The Long View
I have been in technology since before the internet was commercial. I have watched technologies appear, disrupt, fail, and endure. Cryptocurrency — Bitcoin specifically — is in the “endure” category. I said it in 2014 when I first bought Kentino’s earliest hardware, and I will say it again now: this technology stays.
But technology that stays must be approached with the same discipline as any long-term system. You do not build a 25-year platform on shortcuts and quick decisions. You build it on understanding, on good habits, and on having the right people around you when questions arise.
The crypto space is not inherently dangerous. It is inherently new. And new systems always have a learning curve. The people who navigate that curve successfully are not the most technically brilliant — they are the most methodical.Your assets are worth protecting. Your confidence is worth building. And both of those things are easier when you are not doing it alone.