As regulations and privacy laws require ‘reasonable security’, we are seeing more organizations focusing on their duty of care to all interested parties. There are more references to ‘reasonableness’ in breach litigation, and inquiries in how company security programs are implementing reasonable controls.
Professionals seek answers for their specific working environment. Each organization also follows various standards, which can be a challenge. One approach that integrates this process is the Duty of Care Risk Analysis (DoCRA). It provides guidance on how to establish reasonable security.
The DoCRA standard was the risk analysis standard that The Center for Internet Security (CIS) Risk Assessment Method (CIS RAM) is built upon. CIS RAM was developed by HALOCK Security Labs in partnership with CIS.
HALOCK has seen many clients benefit from practicing their duty of care and positive response from legal authorities, regulators, attorneys, business executives, and technical leaders who use this method.
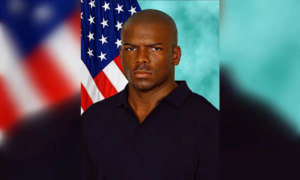
The principal author of the DoCRA standard is Chris Cronin. Chris is a partner at HALOCK and chair of the DoCRA Council and has practiced information security for more than 20 years. He developed Duty of Care Risk Analysis (“DoCRA”) as a method for evaluating whether cybersecurity risks and safeguards are reasonable.
Chris recently answered questions on cybersecurity during a Crain’s Roundtable on Cybersecurity.
What role does your firm play in improving cybersecurity?
Information security consulting firms typically come in two flavors—those that diagnose and prescribe and those that implement. We do both. We’re trusted security advisors to clients, helping them define their acceptable level of risk and establish “duty of care” for cybersecurity.
How can a company decide whether it’s “secure enough” based on its industry, environment and other factors?
Regulations, security standards, and judges all use “reasonable risk” as their determination of what’s “secure enough.” This frustrates people because authorities have not been specific about what “reasonable risk” means until very recently. CIS® has recently published its latest version of their risk assessment method, called CIS RAM v2.1, which shows exactly how to determine whether you’re “secure enough,” and in a way that lawyers, regulators, business executives and information security practitioners can all agree.
Considering recent cyberattacks, have you changed the strategies or advice you offer companies dealing with the new reality?
Our mantra has been, “Log everything you can, starting with what will most likely go wrong.” Logs are always relevant in that we always find new techniques to detect and report suspicious behavior. The information security community has found new ways to detect advanced malware, dangerous servers, suspicious people and unusual user behavior. Of course, this means that you need to analyze your risks so that you understand what’s most likely to go wrong. But this is one of the reasons why risk assessments are so commonly called out in regulations.
What’s your advice about purchasing cybersecurity insurance?
Brokers and carriers are still trying to figure out how to estimate the probability and impact of cybersecurity risk to make the right insurance products for their customers. So, it’s best to work with a broker who wants to work this out with you. Companies should find a carrier interested in “risk engineering.” If you can measure your risk over time as you apply more controls, you can demonstrate to carriers that your risks—and therefore your premiums—should go down.
How are cybersecurity concerns impacting due diligence in M&A transactions?
The more pressing problem recently is, “How do I find hidden liabilities given our limited budget and time for due diligence?” Some acquiring companies try to resolve the uncertainty by adding a cyber insurance policy to the valuation calculation. While there’s wisdom there, the acquiring company can also use some risk analysis more directly by asking whether the target company uses duty of care principles while managing their security program. Because regulators and judges set the price on liability, and because they evaluate reasonableness based on due care principles, a target company will likely hold lower liability by running their security program the way regulators and judges evaluate due care.
What should companies be doing to comply with current—and potential future—cyber-focused legislation?
The open secret in regulations is that they’re very business friendly, and they all demand the same thing—get to reasonable risk. Since Executive Order 12866 was signed in 1993, all regulations require a cost-benefit analysis to make sure that the public is protected from harm, but not by using safeguards that are overly burdensome. This shocks people to hear. But that’s why the words “risk analysis,” “risk assessment,” “reasonable” and “appropriate” pop up so consistently in regulations. Risk analysis is how you do cost-benefit analysis, so do risk assessments the way regulators and litigators understand.
What key cybersecurity elements should C-suite executives and board members be requesting from their IT departments and associated vendors?
Executives own cybersecurity, and therefore must communicate to any team that can create a risk to information and systems—which is everybody—what the organization’s responsibilities are for protecting others and for protecting the organization’s mission and objectives. They must articulate what level of harm they’ll tolerate and what they won’t tolerate. Then they need to work with experts to determine how to measure their performance against those criteria. Finally, management teams need to provide metrics and aggregations or key risk indicators that demonstrate how well the controls work, and how well they’re trending toward acceptable risk. If this sounds lofty, then ask how businesses have managed to do this already with financial reporting, quality management, team performance and more.