Approximately 30,000 websites are hacked globally on a daily basis, with 43% of all cyberattacks targeting small businesses. Such is the scale of the issue that a cyberattack occurs every 39 seconds and costs US$10.5 trillion each year*.
Altoo is an advanced wealth aggregation management system that empowers wealthy individuals and their families to consolidate and interact intuitively with their total wealth. The software company is working to change the tide of cybersecurity threats with industry-leading systems and monitoring. Amongst its many pioneering features include three-factor authentication, while the platform is only accessible via a pre-determined IP address and only once specialist software has been downloaded.
“The cybercrime industry is on a steep rise, as many studies show, and it is now a multi-billion market,” says Stefan Thiel CTO of Altoo.
He adds: “With the Internet of Things, and an ever-increasing number of devices reachable by internet, from everywhere by everyone, the potential threats become even more manifold. Organizations must implement even more robust cybersecurity measures to prevent sophisticated attacks.”
What is Altoo
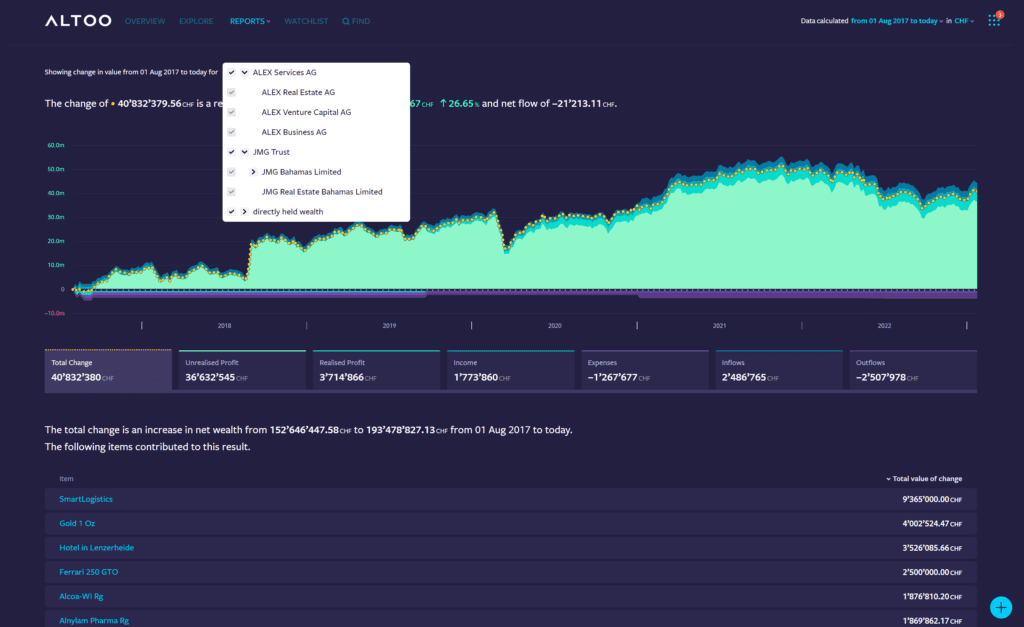
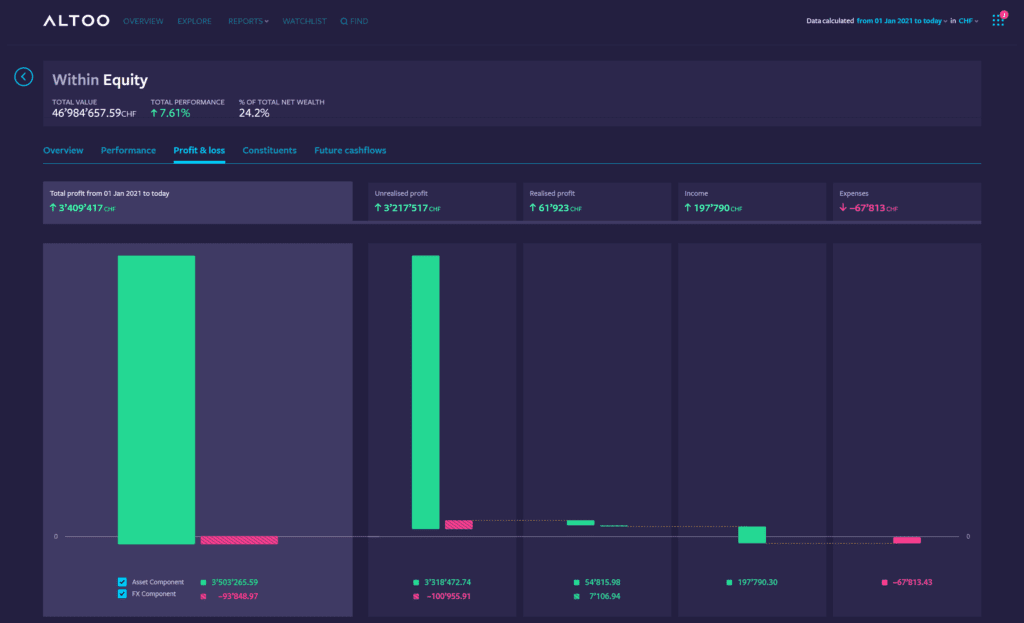
Altoo wealth management software was founded in 2017 by asset owners with years of experience managing multi-generational capital, Altoo empowers wealthy individuals and their families to consolidate and interact intuitively with their total wealth. It offers a personalized easy-to-use dashboard that allows users to view their consolidated assets (bankable and non-bankable) and make decisions based on real-time data.
The platform connects to a user’s bank accounts and portfolios, allowing them to see all their investment activities in one place. The software as a service platform is developed to enable users to save considerable time and effort in understanding the most complex aspects of their global wealth, with the peace of mind that comes from understanding that the highest standards of security and confidentiality protect their information.
Re-imagining online wealth management security
Altoo features highly encrypted communication and storage tools, a very fine granular and sophisticated authorization mechanism, intrusion detection, and advanced security vulnerability testing, to name just a few of its many security features.
Altoo platform is operated in a professional Tier3 data center in Switzerland with all the strict measures that protect physical access to our hardware, Thiel explains. “Additionally, our platform is produced and resides only in Switzerland, and we hire only people based in Switzerland, ensuring a higher level of cyberattack protection.”
He adds: “We monitor thousands of emails daily and have a lot of phishing emails, of which 98% are caught by our email filter. A few sophisticated emails that are able to bypass our systems are often announced to ITOps [IT Operations] by employees or seen by ITOps, and these then help us improve our email filter rules.
“Altoo also have brute force attacks to our platforms (https/443) that try brute force URL scanning. The source IPs of such URL scans are banned after only a very few tries to block extensive misusage.”
Ransom protection is a key part of protecting a system from cyber attacks.
“Ransom is usually also about stealing data and threatening to publish confidential data. That is why we have very sensitive data only in an encrypted manner. Segmentation adds further hurdles for any ransom to spread. We have multiple network segments protected by an internal firewall. Additionally, we use concepts such as “jump hosts” (hardened virtual desktops without access to the internet) to protect sensitive infrastructure.
“Additionally, Altoo uses different OS tools in different segments, which adds further hurdles for any ransom malware to spread. We also have different communication services in different separated locations in case of a [partially] successful attack.”
Protecting yourself online
Thiel recommends that all online users follow a general checklist to protect themselves from cybersecurity attacks. These include:
- Having endpoint device security installed
- Not installing unnecessary applications, especially ones that are for fun
- Exercise caution around freeware – one must understand the motivation/how somebody earns his money; often, freeware is free because the user, his data or behavior, is the product they make money with.
- Stay updated – most serious products will update themselves regularly.
- Don’t fall for any promises – most promises are so primitive, for example, you won’t win a lottery if you did not participate. You won’t inherit from unknown people. The sad thing is that people are still fooled by these phishing emails.
- Finally, keep offline backups of important data.
Thiel also recommends that those at the forefront of preventing cybersecurity stay updated with the latest threats by attending leading industry events. However, he cautions that they should be attended only by those with a full understanding of the industry.
“Security is a major money-making business working with the fears of people that do not understand cybersecurity,” Thiel explains.
“Everything labelled security implicitly has a much higher price. Such conferences provide a very good product and service overview if you know and understand the threats in your situation and your protection needs. One of the key things that security providers do not tell you is that by adding products and services to your dispositive is adding attack points (threat vectors) as well, which you must consider. A good example of this was the 2020 cyberattack on SolarWinds when more than 18,000 customers installed malicious updates,”