In a world where our personal information is constantly at risk, staying safe online has never been more important. One key way to protect yourself is through authentication methods. In this blog post, we dive into the three main types of authentication to help you navigate the digital landscape with confidence and security.
Introduction
In today’s digital age, more and more of our personal information and daily activities are being conducted online. From shopping and banking to socializing and managing important documents, the internet has become an integral part of our lives. However, with this increased reliance on technology comes the risk of cyber threats and attacks. This is where online security becomes crucial.
Online security refers to the measures taken to protect our sensitive information, devices, networks, and systems from unauthorized access or damage. It encompasses a wide range of tactics, including strong passwords, firewalls, encryption techniques, antivirus software, and authentication methods. In this blog post, we will focus on the importance of online security in safeguarding our digital identities.
One of the main reasons why online security is so essential is because it helps prevent identity theft. With the vast amount of personal information available on the internet – from credit card details to social security numbers – cybercriminals can easily gather enough data to steal someone’s identity. This can have serious consequences for individuals as their financial accounts can be emptied or fraudulent purchases made in their name.
Definition and Purpose of Authentication
Authentication is the process of verifying the identity of a user or entity attempting to access a system or resource. In simpler terms, it is the act of confirming that someone or something is who or what they claim to be.
The purpose of authentication is to ensure that only authorized individuals have access to sensitive information and resources. It acts as a gatekeeper, protecting valuable data from unauthorized access and potential security breaches.
Authentication plays a crucial role in maintaining the confidentiality, integrity, and availability of information in both personal and professional settings. It prevents unauthorized users from gaining access to sensitive data, such as financial records, personal emails, or confidential business information.
There are three main types of authentication methods – password-based, multi-factor, and biometric authentication – each with its own unique way of verifying an individual’s identity.
Password-based authentication is the most commonly used method for accessing online accounts and systems. This type of authentication requires users to enter a combination of letters, numbers, and symbols that only they should know. While passwords may seem like a simple solution for securing accounts, they can be easily compromised if not created carefully. That’s why it’s important to use strong passwords that are hard for hackers to guess or crack.
Multi-factor authentication (MFA) adds an extra layer of security on top of traditional password-based authentication. It requires users to provide two or more forms of identification before granting access. This could include entering a one-time code sent via text message or email, using a physical token device that generates codes at regular intervals, or answering security questions.
Biometric authentication uses unique biological characteristics such as fingerprints, facial recognition software, voice recognition technology or iris scans to verify an individual’s identity. Biometrics offer high levels of accuracy since these traits cannot be duplicated easily by others making it difficult for hackers to gain unauthorized access.
Three Main Types of Authentication
Type 1: Single-Factor Authentication
Single-factor authentication, also known as basic or traditional authentication, is the most commonly used method of verifying a user’s identity online. It requires users to provide one form of identification, usually a password, in order to access their accounts or complete transactions.
The process is relatively simple – when you create an account on a website or application, you are asked to choose a unique username and password. The next time you try to log in, all you have to do is enter this information and if it matches the one saved in the system, you are granted access.
While single-factor authentication may seem convenient and easy to use, it has its limitations. First and foremost, it relies solely on something that the user knows – their password. This means that if someone guesses or obtains your password through hacking or phishing attacks, they can easily gain unauthorized access to your account.
Moreover, many people tend to use weak passwords that are easy for hackers to guess. Commonly used passwords such as “123456” or “password” can be easily cracked by automated programs designed for this purpose.
To address these issues and enhance security levels, many websites now require users to create complex passwords with a combination of letters (both upper and lower case), numbers and special characters. Some may also ask for additional personal information like date of birth or answer security questions in case you forget your password.
Examples (passwords, PINs)
Examples of passwords and PINs are the most common forms of authentication used in our daily lives. They act as a safeguard for our personal information and help us access various online accounts such as email, banking, shopping, and social media platforms. However, with the increasing number of cyber threats, it is crucial to understand the importance of creating strong and unique passwords or PINs.
Passwords are strings of characters that are used to verify a user’s identity when logging into an account. They can be a combination of letters, numbers, and special symbols. A strong password should be at least 8-12 characters long and include a mix of upper and lower case letters, numbers, and symbols. It should also not contain easily guessable information such as names, birthdates or common words.
Here are a few examples of good passwords:
1) P@$$w0rd! – This password follows all the guidelines mentioned above.
2) Tr!3ngL3$S16ht – This password has 15 characters with a mix of uppercase letters, lowercase letters, numbers, and symbols.
On the other hand, PINs (Personal Identification Numbers) are typically four to six-digit codes that provide access to electronic devices or services such as ATM machines or mobile phones. Unlike passwords that can be any length and combination of characters, PINs have limited options since they usually only consist of numbers.
Here are some examples of good PINs:
1) 9425 – This PIN may seem random but it actually represents “W-H-A-T” on your phone keypad.
2) 3579 – This sequence follows an ascending pattern which might make it easy for you to remember.
Type 2: Two-Factor Authentication
Two-factor authentication, also known as multi-factor authentication, adds an extra layer of security to the traditional username and password login process. It requires users to provide a second form of identification, making it more challenging for hackers to gain unauthorized access.
The first factor of authentication is typically something you know – your password or PIN. The second factor can be something you have or something you are. This could include a physical device like a phone or token, biometric data such as fingerprint or facial recognition, or even a one-time code sent via email or text message.
This type of authentication is highly effective because even if someone manages to obtain your password, they will still need the second factor to access your account. This significantly reduces the chances of successful hacking attempts.
There are various types of two-factor authentication methods available, including SMS-based codes, authenticator apps like Google Authenticator or Authy, hardware tokens like YubiKey, and biometric verification. Each method offers different levels of security and convenience.
SMS-based codes involve receiving a unique code via text message that needs to be entered along with the password during login. While this method may seem convenient as it does not require any additional devices, it has some vulnerabilities. Hackers can intercept these codes through SIM swapping attacks or phishing scams.
Examples (SMS codes, biometrics)
Examples of authentication methods include SMS codes and biometrics. These are popular forms of authentication that are commonly used in various online platforms and applications.
SMS codes, also known as one-time passwords (OTP), are a form of two-factor authentication. They involve sending a unique code to the user’s mobile phone via text message. This code is then required to be entered along with the usual login credentials, providing an extra layer of security. The idea behind this method is that only the person with access to the registered phone number can receive the code and enter it correctly. Therefore, even if someone has obtained your login information, they will not be able to access your account without having your phone in their possession.
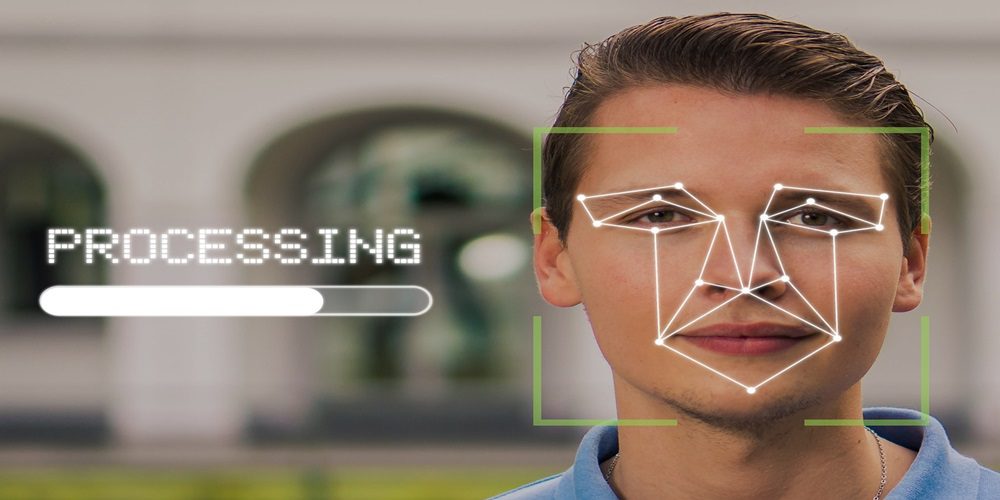
Biometric authentication is another popular method used for online security. It involves using physical characteristics or behavioral patterns unique to an individual as a means of identification. This could include fingerprints, facial recognition, voice recognition, or even iris scanning. Biometric data cannot be easily replicated or stolen like passwords or PINs, making it a more secure form of authentication.
One example of biometric authentication widely used today is fingerprint scanners on smartphones. Many smartphones now come equipped with fingerprint sensors that allow users to unlock their devices by simply placing their finger on the scanner instead of entering a password or PIN every time.
Another example is facial recognition technology, which uses algorithms to map out and identify key features on a person’s face for verification purposes. This method has become increasingly popular for unlocking smartphones and other devices, making it easier for users while still maintaining high levels of security.
Type 3: Multi-Factor Authentication
Multi-factor authentication (MFA) is a security process that requires users to provide two or more forms of identification before they can access an account or system. This type of authentication is becoming increasingly popular due to its effectiveness in preventing unauthorized access and protecting personal information from hackers.
There are three main factors involved in multi-factor authentication – something you know, something you have, and something you are. Let’s explore each factor in detail:
1. Something You Know
This refers to the traditional method of authentication, where users enter a password or PIN to gain access. While passwords are still commonly used, they are not as secure as they used to be due to the rise of hacking techniques such as phishing and brute force attacks. However, when combined with other factors, passwords can add an extra layer of security.
2. Something You Have
This factor involves using a physical device or token as proof of identity. This could be a smart card, USB key, or even your smartphone. These devices generate one-time codes that are required along with your password for login purposes. The advantage of this method is that even if someone manages to obtain your password through hacking or theft, they would still need the physical device to gain access.
3. Something You Are
This factor utilizes biometric data such as fingerprints, facial recognition, voice recognition, or iris scans for authentication purposes. Biometric data is unique and cannot be easily replicated by others making it highly secure method of authentication.
The combination of these three factors makes it extremely difficult for hackers to gain access to your accounts or systems without proper authorization.
Examples (smart cards, facial recognition)
Smart cards are a type of physical token that stores digital information and can be used for authentication purposes. These small plastic cards contain an embedded microchip that holds encrypted data, making it difficult for hackers to access or replicate the information stored within them. Smart cards often require a PIN or password to be entered in order to access the data stored on the chip, adding an extra layer of security.
A common example of smart card usage is in banking systems, where customers use their debit or credit card with a chip to make secure transactions at ATMs or point-of-sale terminals. Another application is in government-issued identification cards such as passports or driver’s licenses, which use smart card technology to store biometric information like fingerprints or facial images for identification purposes.
Facial recognition is another form of biometric authentication that has gained popularity in recent years. This technology uses unique facial features such as bone structure and skin texture to verify a person’s identity. Facial recognition software captures an individual’s face from different angles and compares it to a pre-stored image in its database.
One major advantage of facial recognition is convenience – there are no physical tokens required as everything relies on capturing your face through a camera device. It also eliminates the need for remembering passwords or PINs which can be easily forgotten or stolen by hackers.
Conclusion
authentication is an essential aspect of staying safe online. As technology continues to advance and our lives become more intertwined with the digital world, it is crucial to have strong authentication methods in place to protect our personal information and sensitive data.