These days, encryption in transit and encryption at rest is commonplace, yet they are insufficient to safeguard your data. However, your data is not secure when it is encrypted at rest and is stored on servers. Once a hacker has gained access to the server, they are free to stay and read the messages for as long as they like.
This is why end-to-end encrypted emails have become popular in recent times, as it offers the most advanced level of communication security. The sender and the intended recipient are the only parties with access to the data in an end-to-end encrypted system; everyone else is prohibited. The server’s encrypted data is protected from access by hackers and other undesirable parties.
What is end-to-end encryption?
Any type of data can be converted from a readable format to an unreadable format using end-to-end encryption. As a result, potential listeners can only obtain material that has been jumbled and rendered unintelligible. With the aid of the matching decryption key, only the recipient may decrypt the data.
No one can read the encrypted text when end-to-end encryption is used, not even telecom companies, internet service providers, or the communication service provider itself. The sender and the intended recipient are the only parties with access to the data in an end-to-end encrypted system; everyone else is prohibited.
How does end-to-end encryption work?
Technically speaking, public key cryptography only allows for the matching of one private key to each public key. Messages are encrypted and decrypted using these keys. If you use someone’s public key to encrypt a message, they can only decode it if they have the corresponding private key. Data is converted into an unreadable format during encryption.
From that point forward, any unauthorized entity that obtains the data will not be able to read the messages sent or even decrypt the encrypted data. It is also important to ensure that the data must be encrypted such that only the intended receiver can decrypt it and restore it to a readable state.
What are the benefits of using end-to-end encrypted emails?
-
- Improved user experience: The process of sending and receiving encrypted emails might be made simpler if the software used to encrypt and decrypt emails is more user-friendly and simple to use.
- Better integration with existing email systems: People would find it simpler to use end-to-end encrypted email systems without moving between multiple apps or programs if they were better integrated with current email systems.
- Greater awareness and education: End-to-end encrypted email may become more popular and simpler to use if more people are aware of its advantages and know how to use it properly.
- More widespread adoption: The availability and usability of end-to-end encrypted email would increase if more email providers and businesses made it a regular feature.
- Avoid identity theft: People are extremely vulnerable to identity theft when their credentials are not encrypted and shared through email. By using end-to-end encryption, you can make emails unreadable to everyone but the intended recipient.
Problems in end-to-end encryption of emails
End-to-end encrypted email can be challenging as both the sender and the recipient require specialist software that both encrypts and decrypts messages. Moreover, for communication to occur, both parties must securely exchange their encryption keys.
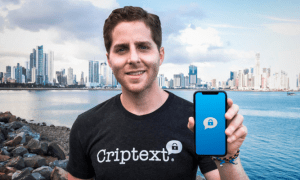
Encrypted Space: Simplifying End-to-End Encrypted Email
Encrypted Spaces is a 100% free-to-use software that simplifies end-to-end encrypted email with spaces. Each space is assigned a shared and secret key. The sending space’s secret key and the receiving space’s public key are used to encrypt the data being sent. The public key of the sending space and the secret key of the receiving space is used to decrypt the received data. Encrypted data is removed after delivery, much like WhatsApp.
Encrypted Space software can encrypt everything from name, subject, body, and files to ensure that sending even sensitive emails over unsecured networks would no longer give you sleepless nights. Started as a way to secure medical records, today, Encrypted Spaces is used for all kinds of industries, including IT, call centers and more.